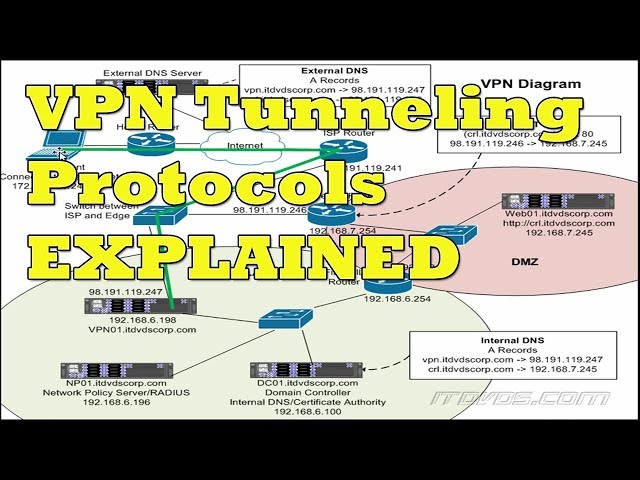
How Tunneling Is Accomplished in a VPN – When a user activates a VPN, a secure tunnel is created between the user’s device and the VPN server.
 Checkout this video:
Checkout this video:
Introduction to VPN Tunnels
In order to understand how a VPN tunnel is established, it is important to first understand the concept of encapsulation. Encapsulation is the process of taking data from one protocol and encapsulating it into another protocol. In the case of a VPN tunnel, the data is encapsulated from a higher-level protocol such as TCP/IP into a lower-level protocol such as L2TP or PPTP.
What is a VPN Tunnel?
A VPN tunnel is a private path through the public network (Internet). Data is encrypted as it travels through this tunnel, ensuring that anyone intercepting the data cannot read it. This provides a high level of security when you are sending confidential data over the Internet, such as credit card numbers or passwords.
How Does a VPN Tunnel Work?
A VPN tunnel is created when data packets are encrypted and then sent through a public network, such as the Internet, to a private network, such as a company’s intranet. The process of encapsulating data packets in an outer layer of encryption is known as “tunneling.”
Tunneling is accomplished by encapsulating the data packet within another data packet, which is then encrypted. This outer packet has a header that includes information about the destination of the inner packet, as well as the encryption method used. The inner packet is then decrypted by the receiving computer and forwarded to its intended destination.
VPN tunneling provides a number of advantages for both individuals and businesses. First, it allows users to connect to a private network from a public location, such as an Internet cafe or airport. This allows them to access their company’s resources, such as email and file servers, while still maintaining a high level of security. Second, VPN tunneling can be used to create secure connections between two or more private networks. This can be useful for businesses that have multiple locations and need to share resources between them.
Types of VPN Tunnels
Tunneling is the process of sending encapsulated data through an untrusted network. A VPN tunnel allows two endpoints to securely communicate with each other over an untrusted network, such as the Internet. There are two types of VPN tunnels: point-to-point and multipoint.
Point-to-Point Tunneling Protocol (PPTP)
Point-to-Point Tunneling Protocol (PPTP) is a method for implementing virtual private networks. PPTP uses a control channel over an IP network to create and maintain a tunnel between two remote locations. Point-to-Point Tunneling Protocol is most commonly used with dial-up Internet services, but can also be used to connect LANs.
In order to set up a VPN, each computer on the network must have PPTP software installed. Once the connection is made, data can be exchanged between the two computers as if they were on the same LAN. Data traveling between the two machines is encrypted and masqueraded so that it appears to be coming from a single IP address.
One advantage of using PPTP is that it does not require special hardware or software at either end of the connection. In addition, it is easy to configure and does not require any changes to existing networking infrastructure.
Layer 2 Tunneling Protocol (L2TP)
L2TP is a combination of two older technologies, PPTP from Microsoft and L2F from Cisco. L2F was never implemented as a stand-alone protocol but was used as the basis for PPTP. Cisco systems still use L2F internally on some of their equipment. L2TP uses UDP port 1701 and can be configured to run on most firewalls and routers without the need to make additional holes in the firewall or router.
L2TP uses the concept of tunnels to send data. A tunnel is simply a connection between two points on a network. In order for data to be sent through a tunnel, the sending computer (the initiator) must first establish the tunnel with the receiving computer (the responder). Once the tunnel is established, data can be passed through it. In order for this to work, both computers must have an L2TP client program installed and configured.
Most L2TP implementations also support Microsoft’s Point-to-Point Tunneling Protocol (PPTP). PPTP uses different encapsulation methods than L2TP, so L2FP will often be transparently passed through devices that do not support it themselves. This makes it possible to use PPTP tunnels over non-Microsoft systems such as Linux or Mac OSX.
Internet Protocol Security (IPsec)
IPsec is a protocol suite that authenticates and encrypts the packets of data sent over an IP network. IPsec uses two security protocols, Authentication Header (AH) and Encapsulating Security Payload (ESP), to provide data integrity, confidentiality, and authentication. AH verifies the authenticity of data at the IP layer, while ESP encrypts and authenticates data at the transport layer. Both AH and ESP can be used together or independently.
Setting up a VPN Tunnel
Tunneling is the process of encapsulating Internet Protocol (IP) datagrams within an IP datagram. The encapsulation is accomplished by creating a tunnel, which is like a virtual pipe, that links two nodes or two networks together. The most common type of tunneling is Point-to-Point Tunneling Protocol (PPTP), which is used to create a VPN tunnel between two nodes.
Installing the VPN Client
1. To begin, you will need to install the VPN client on your device. You can usually find this software on the website of your VPN provider.
2. Once you have downloaded the client, run the installation file and follow the prompts.
3. Some clients may require you to enter a activation code, which you should be able to find in your provider’s documentation or customer support portal.
4. After the installation is complete, launch the client and sign in with your VPN credentials.
5. Once you are logged in, you should see a list of server locations that you can connect to. Select one and click “Connect”.
6. Depending on your provider and protocols supported, you may be asked to select additional options at this point. For example, you may need to choose between “Tunnel all traffic” or “Split tunneling” mode.
7. After making your selections, click “OK” or “Connect” to establish the VPN connection.”
Configuring the VPN Client
A Virtual Private Network (VPN) can be setup in different ways. The most common method is where a VPN client on the user’s computer sends all of the user’s traffic through an encrypted tunnel to the VPN server. This is known as “tunneling” and is accomplished by configuring the VPN client software on the user’s computer.
There are two components to setting up a tunneled VPN connection: authentication and encryption. Authentication is used to verify that the VPN client is authorized to access the VPN server, and encryption is used to protect the information being sent through the tunnel from being read or modified.
When configuring a VPN client, you will need to specify the following information:
-The IP address or hostname of the VPN server
-The type of encryption that will be used
-The User ID and password (or other form of authentication) that will be used to authenticate with the VPN server
Connecting to the VPN Server
A client connects to the VPN server at a public IP address. The client may be a laptop, desktop, smartphone, or tablet. The client software installed on the device uses the public IP address to connect to the VPN server. The VPN server sees the public IP address of the client and uses it to identify which internal private IP address to assign to the client.
The client software installed on the device uses encryption algorithms to protect data traveling from the client device to the VPN server. Data traveling from the VPN server to the destination website or cloud application is not encrypted because it is already on a private network inside of the corporate firewall.
The source port number is changed by tunneling software on the client device to a destination port number known by the tunneling software on the VPN server. The destination port number allows traffic from multiple clients going to different websites or cloud applications to be multiplexed together on a single public IP address on the corporate firewall. This is known as port forwarding and is transparent to users because they continue using their web browser or cloud application in uninterrupted fashion.
##Topic: 3 Different Types of External Hard Drives
##Heading: 3 Different Types of External Hard Drives ##Expansion:
External hard drives come in all shapes and sizes, but there are three main types: portable, desktop, and NAS (network-attached storage). Here’s a quick rundown of each so you can decide which one is right for you.
Portable external hard drives are compact and easy to carry, making them ideal for traveling with your laptop or taking your music collection with you on your phone. However, they generally have less storage capacity than other types of external hard drives and can be more expensive per gigabyte.
Desktop external hard drives are larger and require their own power supply, but they offer more storage capacity for your money than portable hard drives. They’re not as convenient for traveling, but they’re great for backing up your computer or storing media files such as music, videos, and photos.
NAS (network-attached storage) devices are designed for use with home networks and can be used by multiple devices at once. They’re generally more expensive than other types of external hard drives, but they offer features such as streaming media support and remote access that make them worth considering if you have a need for them.
Conclusion
In conclusion, we have seen that tunneling is a technique used to send data securely over a public network by encapsulating the data in a private envelope. Tunneling can be used to send data over networks that are not secure, or to connect two networks that are not compatible. VPNs use tunneling to send data securely over the internet.
